
Verizon’s just-released 2023 Data Breach Investigations Report shows the continued effectiveness of business email compromises. The study, which tracked incidents occurring between November 1, 2021 and October 31, 2022, found that BEC attacks doubled and represented more than 50% of social engineering attacks. The global study included incidents in the Asia-Pacific regions, EMEA, North America, and Latin America.
BECs have evolved to include several sophisticated gambits, including one recently reported by Avanan, a unit of Check Point Software, involving the use of legitimate services, like Dropbox, to hide malware.
The study offered a broad look at actors, actions, trends and incidents across industries, noting that public administration (3,270 incidents), information (2,105), finance (1,829) and manufacturing (1,814) are the sectors that experienced the highest numbers of incidents over the period.
The report offered these major findings:
- 74% of all breaches included the human element, with people being involved either via error, privilege misuse, use of stolen credentials or social engineering.
- 83% of breaches involved external actors, and the primary motivation for attacks continues to be overwhelmingly financially driven (95%).
- The three primary ways in which attackers access an organization are stolen credentials, phishing and exploitation of vulnerabilities.
Jump to:
- Social engineering pretexts trick users into dropping credentials
- Financial gain trumps politics in exploits
- DDoS tops the list of attack patterns
- Use of stolen credentials drives web application attacks
- Insiders, yes, but mostly external actors
- Stolen credentials: The most common action
- Attacked assets led by web servers
Social engineering pretexts trick users into dropping credentials
Built upon analysis of 953,894 incidents, of which 254,968 are confirmed breaches, the Verizon study found that 50% of all social engineering incidents during the study period used pretexting, a phishing tactic that involves tricking someone into giving up information that may result in a breach. According to the study, the practice, which is commonly used in BEC attacks, doubled in volume compared to the prior year’s.
Verizon reported 1,700 social engineering incidents overall, with attackers most often using it to steal credentials (Figure A).
Figure A
SEE: Half of companies tracked in a new study were hit by spearphishing campaigns (TechRepublic)
Financial gain trumps politics in exploits
An uptick in espionage and state-aligned actors notwithstanding, the Verizon study reported that financial motives were behind 94.6% of breaches, with organized crime being the most prevalent threat actor.
The authors of the study also reported a fourfold increase this year in the number of breaches involving cryptocurrency compared to the prior year’s recorded breaches. “That is a far cry from the days of innocence in 2020 and earlier, when we got one or two cases maximum each year,” they wrote.
Verizon reported the percentages of financially motivated attacks by category:
- System intrusions: 97%, with only 3% aimed at espionage.
- Social engineering exploits: 89%, with 11% aimed at espionage.
- Basic web application attacks: 95%, with 4% aimed at espionage.
- Lost and stolen assets: 100% financial gain.
DDoS tops the list of attack patterns
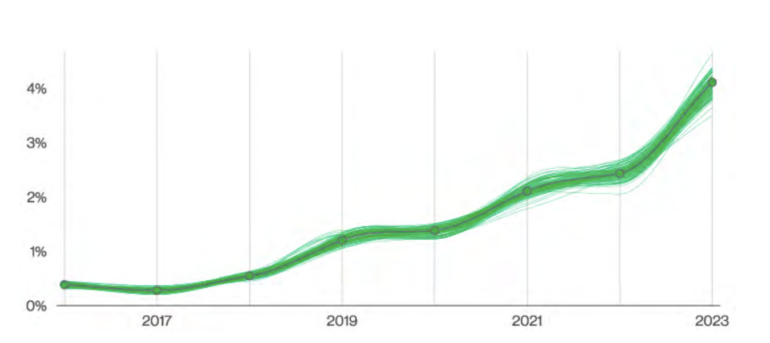
Verizon reported 6,248 distributed denial of service incidents. The study’s authors noted the brute force DDoS tactic called DNS water torture reportedly grew in prevalence (Figure B).
Figure B
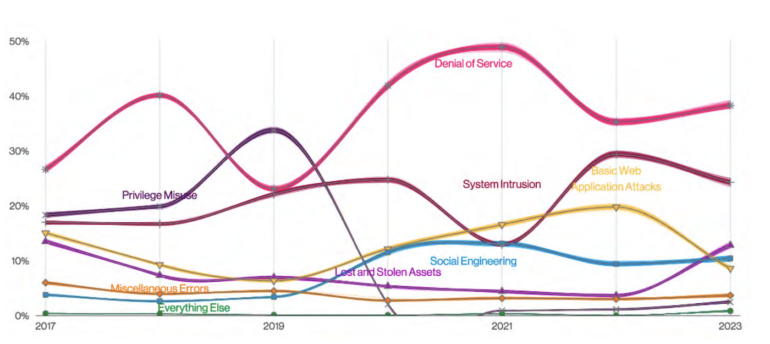
“A point of attention that some of our partners brought to us was the growth of distributed DNS Water Torture attacks in, you guessed it, shared DNS infrastructure,” the study authors wrote, noting the attacks are a resource exhaustion attack done by querying random name prefixes on the DNS cache server so it always misses and forwards it to the authoritative server.
According to the study, there were 3,966 system intrusion incidents involving attacks using malware to breach organizations, which often resulted in the delivery of ransomware. In 34% of cases, data compromised was personal in nature, followed by system data, and finally internal data.
SEE: Web users are not very aware of their data footprints. (TechRepublic)
Use of stolen credentials drives web application attacks
About one quarter of Verizon’s dataset for its study involved basic web application attacks, 86% of them using stolen credentials, which attackers employ to gain access to enterprises. The study reported 1,404 such incidents over its period of observation, with 86% aimed at credential theft, 72% for personal data and 41% seeking internal data.
Verizon also recorded 602 miscellaneous errors that include misconfigurations often committed by system administrators and developers. The study reported that 99% of these errors were internal, with 89% of compromises involving personal data.
Insiders, yes, but mostly external actors
Attackers on the outside were responsible for 83% of breaches, while internal actors (deliberately or inadvertently) accounted for 19% of breaches, according to Verizon. The report’s authors said 62% of all incidents were committed by organized crime.
Stolen credentials: The most common action
Nearly half of breaches in the study period involved theft of credentials, with delivery of ransomware being the central action in just over 20% of breaches. Phishing was the action attackers took in 12% of external attacks, followed by breaches, in which the actions attackers focused on were:
- Pretexting
- Exploiting vulnerabilities
- Creating misdeliveries
- Abusing privilege
- Installing a backdoor
- Exfiltrating data
- Scanning networks
Attacked assets led by web servers
The vast majority of attacks tracked by Verizon (83%) affected servers. Only 20% of attacks affected people directly. A decreasingly small percentage of attacks impacted media, kiosks and terminals, networks and embedded systems.








